Grab a tin foil hat, your TV is watching you.

The opinions expressed in this article reflect those of the author, Tom Dodd, and not entrustIT
In the past, if you claimed that the Government was listening into your conversations through your TV, you might be placed in a straitjacket and carted off to the nearest mental health facility. Unfortunately, thanks to a huge data release by WikiLeaks this week, your claims would be entirely justified.
As a consumer, you may have heard of the “internet of things”. Perhaps you scoffed at the thought that your fridge needs an internet connection. The principle is that the internet of things allows us the ability to control aspects of our appliances from our smartphones. Modern appliances are becoming internet enabled and we are each being pushed to embrace a ‘smart home’, whereby our computers, televisions, lights, heating and even door locks can be controlled via apps on our smartphones. The theory sounds great, but the reality may be far darker.WikiLeaks creates more headaches for the Government
On 7th March, WikiLeaks issued a press release codenamed “Vault 7”. In it are details of the CIA’s cyber-weapons programme, called ‘zero day’. These include malware, viruses and Trojans. The several hundred million lines of code included in zero day give the possessor the entire hacking capacity of the CIA. The leak even reveals a tool to listen in on conversations using smartphone or smart TV microphones. What’s more, the CIA (and GCHQ) appear to have been extremely irresponsible with the handling of these tools.
After the Edward Snowden leaks, the Obama administration promised that security vulnerabilities discovered by intelligence services would be released to the US based tech manufacturers on an ongoing basis. The Vault 7 leak shows that the CIA has instead been hoarding discovered vulnerabilities – presumably since they wanted them to remain open. The trouble is, if US intelligence agencies are aware of these flaws, is it not reasonable to assume that other agencies are too? Or that they will be in the future?
By discovering these flaws (in popular operating systems such as Windows, iOS, MacOS and Android) and opting not to inform the developers, they remain open to exploitation – including by those who seek to do harm. Specific CIA malware revealed in the leak is even able to penetrate both iPhone and Android software running presidential Twitter accounts. Given President Trump’s love affair with Twitter, and that one tweet from his account has the power to send stock prices plummeting, or worse still, potentially start a war, how valuable is that malware to a dangerous hacker?
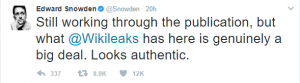
Edward Snowden has had his say on the leaks
A difficult balancing act
Balancing public safety with public freedom is a difficult process. You may feel entirely relaxed about the intelligence agencies’ ability to hack into your TV if it means that you don’t become a victim of terrorism. However, in an effort to protect the public from violent terrorism, the CIA has left the public open to cyber terrorism. Some would argue that cyber weapons have the potential to deal more damage than conventional weapons. Once malicious code is out there, it is relatively easy to copy and extremely difficult to control. The very fact that this latest leak has been released indicates that the CIA and NSA cannot keep control of their sensitive data.
To be concerned about dangerous hacking tools falling into the wrong hands, or the possibility that you could be spied on in your own home is no longer a paranoid delusion. The threat is very real. The agencies that exist to protect us have left us vulnerable as a result of their recklessness.
The Bottom Line
Vault 7 is a goldmine of information – and it is damning for the agencies involved. Not only have intelligence agencies been working hard to discover vulnerabilities to spy on citizens, they have kept them to themselves – leaving them open to be exploited by hackers and terrorists. Whilst it is entirely justified to monitor terrorists, who determines who is a terrorist? How broad is that definition? We must be careful that we do not let intelligence agencies abuse the threat of terror to justify robbing us of our freedom.
In the short term, we can expect to see major tech companies patching the vulnerabilities exposed in Vault 7. Yet, we now have an idea of the lengths major intelligence agencies will go to in order to harvest information. More vulnerabilities will be found, and likely hoarded, until they are again exposed. The public should not sit by and accept that this a reality of modern life. These agencies must be held accountable for their failings.
The press release of Vault 7 can be found here. If you have an interest in cyber security – it is worth reading.
Subscribe here!
Recent Posts
Posts by tag
- technology (131)
- Security (115)
- cyber security (103)
- IT Security (101)
- Managed Service (75)
- modern technology (73)
- IT support (70)
- Microsoft 365 (69)
- Cloud (66)
- business (66)
- cyber attack (63)
- cloud computing (60)
- cybersecurity (58)
- workplace (57)
- cloud it (56)
- microsoft (56)
- IT (54)
- Microsoft Teams (54)
- Working from home (51)
- productivity (49)
- office (46)
- office 365 (45)
- Password Security (44)
- entrustit (42)
- Cyber (41)
- employees (39)
- Uncategorised (38)
- flexible work (37)
- Remote (33)
- efficiency (32)
- it support bournemouth (31)
- Hosted Workspace (30)
- cyber privacy (30)
- hosted desktop (30)
- schools (29)
- email security (28)
- independent schools (28)
- it support dorset (28)
- it support hampshire (27)
- school ict (27)
- collaboration (26)
- computing (26)
- 2023 (25)
- msp (24)
- public cloud (24)
- it consultancy (22)
- IT audit (21)
- it support southampton (21)
- entrust (20)
- it consultancy bournemouth (20)
- password (20)
- it consultancy dorset (19)
- it consultancy hampshire (19)
- it support winchester (19)
- passwords (19)
- ransomware (19)
- hacking (18)
- hosted applications (18)
- VoIP (17)
- cloud cctv (17)
- cloud voip (17)
- covid19 (17)
- data (17)
- it consultancy southampton (17)
- private cloud (17)
- IT costs (16)
- cctv (16)
- network (16)
- teamwork (16)
- Coronavirus (15)
- hackers (15)
- office 365 support (15)
- GDPR (14)
- internet (14)
- Protection (13)
- covid-19 (13)
- hack (13)
- hardware (13)
- internet safety (13)
- management (13)
- vulnerabilities (13)
- Hosted Desktop and Applications (12)
- Windows Virtual Desktop (12)
- awards (12)
- hybrid cloud (12)
- windows 10 (12)
- 2020 (11)
- 2022 (11)
- Microsoft Planner (11)
- artificial intelligence (11)
- data breach (11)
- phishing (11)
- AI (10)
- Hampshire (10)
- IT Director (10)
- digital (10)
- planning (10)
- uk (10)
- windows (10)
- Backup (9)
- Cyber Essentials (9)
- attack (9)
- award winning (9)
- bitwarden (9)
- eu (9)
- partnership (9)
- software (9)
- telephony (9)
- usecure (9)
- communication (8)
- desk phone (8)
- education (8)
- infrastructure (8)
- outsource (8)
- staff (8)
- Access Management (7)
- Bournemouth (7)
- Cyber Essentials Plus (7)
- Dorset (7)
- Google (7)
- IP (7)
- Multi-Site Business (7)
- OneDrive (7)
- award (7)
- cloud storage (7)
- european union (7)
- legal (7)
- mobile (7)
- offsite backup (7)
- sme (7)
- 2019 (6)
- AI CCTV (6)
- Apple (6)
- ISO (6)
- News (6)
- Risk assessment (6)
- Skype for Business (6)
- apps (6)
- architect (6)
- child protection (6)
- hacks (6)
- internet of things (6)
- iot (6)
- legal it (6)
- mobile phones (6)
- modern work (6)
- onsite backup (6)
- password manager (6)
- remote desktop service (6)
- resources (6)
- virus (6)
- 3d design desktop (5)
- Azure (5)
- Case Studies (5)
- Desktop (5)
- Microsoft Copilot (5)
- Thames Valley Tech & Innovation Awards (5)
- The Business Magazine (5)
- Windows 7 (5)
- brexit (5)
- designer (5)
- ios (5)
- legacy (5)
- personal data (5)
- proactive (5)
- smartphone (5)
- sophos (5)
- surrey (5)
- united kingdom (5)
- website (5)
- Attacks (4)
- BYOD (4)
- ChatGPT (4)
- DR (4)
- DR planning (4)
- Facebook (4)
- Government (4)
- High Growth (4)
- MDR (4)
- Managed Service Provider of the Year (4)
- Microsoft Forms (4)
- SharePoint (4)
- Tech Growth (4)
- VPN (4)
- WannaCry (4)
- Zoom (4)
- acquisition (4)
- budgets (4)
- computer performance (4)
- ddos (4)
- digital transformation (4)
- disaster recovery (4)
- law (4)
- meetings (4)
- online meetings (4)
- remote learning (4)
- strategy (4)
- windows 11 (4)
- wireless internet bournemouth (4)
- wireless internet southampton (4)
- 2021 (3)
- 2024 (3)
- 5G (3)
- Dorset Chamber (3)
- EDR (3)
- Fourth Industrial Revolution (3)
- General (3)
- Google Drive (3)
- Hampshire Chamber (3)
- Help (3)
- Local (3)
- Microsoft Autopilot (3)
- NHS (3)
- New Forest (3)
- South Coast Tech & Innovation Awards (3)
- Tech Company of the Year (3)
- Thames Valley (3)
- Tiva (3)
- b2b (3)
- big switch off (3)
- business growth (3)
- citrix (3)
- closed cloud (3)
- connectivity (3)
- copilot (3)
- copilot pro (3)
- digital hub (3)
- guide (3)
- innovation (3)
- instagram (3)
- intelligence (3)
- london (3)
- smart buildings (3)
- storage (3)
- teaching (3)
- trump (3)
- twitter (3)
- video conferencing tools (3)
- zero touch deployment (3)
- zero-trust (3)
- 2016 (2)
- 2018 (2)
- BGL Company (2)
- Bourne Group (2)
- Burhill (2)
- Burhill Group (2)
- CAD (2)
- Central South Business Awards (2)
- Cloudtango (2)
- Environment (2)
- Firewall (2)
- GPT-4 (2)
- Gen Z (2)
- Hampshire Business Awards (2)
- ISBA (2)
- IT strategy (2)
- Macs (2)
- Mr Mulligans (2)
- PaaS (2)
- Privacy Shield (2)
- Sydenhams (2)
- Wifi (2)
- XDR (2)
- afc bournemouth (2)
- afcb (2)
- android (2)
- bcs (2)
- berkshire (2)
- best msp hampshire (2)
- best msp uk (2)
- blockchain (2)
- broadband (2)
- camcloud (2)
- cryptocurrency (2)
- dark web (2)
- downtime (2)
- dropbox (2)
- eagle eye networks (2)
- east grinstead (2)
- exhibition (2)
- farnham (2)
- finalist (2)
- it support surrey (2)
- it support sussex (2)
- legalex (2)
- machine learning (2)
- macos (2)
- organisation (2)
- paypal (2)
- predictions (2)
- president (2)
- reading (2)
- serval systems (2)
- smart sensors (2)
- solent (2)
- us (2)
- utility management (2)
- 1998 (1)
- 2026 (1)
- AMD (1)
- ARM (1)
- Abbey Hill (1)
- Aldwickbury Park (1)
- BBC (1)
- BUNKERS! (1)
- Bedford (1)
- Bedfordshire (1)
- Birchwood Park (1)
- Burnout (1)
- CEO (1)
- Cloud VMS (1)
- Comms Dealer (1)
- East Midlands (1)
- Endpoint 100 (1)
- Go Integrator (1)
- Growth 100 (1)
- Harvey Jones Kitchens (1)
- Hoebridge (1)
- Hospitality (1)
- IT satrategy (1)
- Ignite 2018 (1)
- Ignite 2020 (1)
- Insider (1)
- Intune (1)
- Jeff Dodd (1)
- LLM (1)
- Leaders (1)
- Loop (1)
- M&A (1)
- MFA (1)
- MPLS (1)
- MSP Select 2024 (1)
- Market (1)
- May (1)
- Multi Factor Authentication (1)
- MyAnalytics (1)
- Ninja Warrior UK (1)
- PBX (1)
- PM (1)
- Power BI (1)
- Ramsdale Park (1)
- Redbourn (1)
- Regulation (1)
- Reid Steel (1)
- SD-WAN (1)
- Surrey Business Awards (1)
- Thornbury (1)
- WCry (1)
- WannaCrypt (1)
- Windows Autopilot (1)
- Wycombe Heights (1)
- ashley madison (1)
- bandwidth (1)
- battersea (1)
- beach (1)
- big data (1)
- black friday (1)
- bloatware (1)
- brand (1)
- builders merchant (1)
- business process audit (1)
- cambridge analytica (1)
- canada (1)
- cia (1)
- clinton (1)
- cnn (1)
- co op (1)
- compliance (1)
- copyright (1)
- crime (1)
- customer service (1)
- cyber monday (1)
- cyber resilience act (1)
- dean drako (1)
- defence (1)
- dkim (1)
- dmarc (1)
- dns (1)
- donald (1)
- dyn (1)
- election (1)
- enterprise (1)
- entrustIT Community Champions (1)
- epos (1)
- equality (1)
- executive order (1)
- facial recognition (1)
- fax (1)
- football (1)
- gchq (1)
- grinstead (1)
- hiring (1)
- intel (1)
- intercept x (1)
- interview (1)
- it support bedfordshire (1)
- josh widdicombe (1)
- knights of old (1)
- landmarks (1)
- learning (1)
- legal technology forum (1)
- leisure (1)
- meltdown (1)
- millennials (1)
- mimecast (1)
- mirai (1)
- msp select 2026 (1)
- no-deal (1)
- number plate detection (1)
- onsite (1)
- outsourcing (1)
- paper (1)
- patisserie valerie (1)
- performance reviews (1)
- pound (1)
- premier league (1)
- private equity (1)
- procrastination (1)
- qualys (1)
- recruitment (1)
- research (1)
- retail (1)
- roundtable (1)
- samsic (1)
- sharefile (1)
- smishing (1)
- snowden (1)
- solent business awards (1)
- solentBA (1)
- spectre (1)
- spf (1)
- sterling (1)
- storm (1)
- structured cabling (1)
- talktalk (1)
- top msp (1)
- trumppresident (1)
- ukitawards (1)
- united states (1)
- usa (1)
- vault 7 (1)
- vitality stadium (1)
- vulnerability scanning (1)
- whatsapp (1)
- white (1)
- white house (1)
- wikileaks (1)
- women in business (1)
- xiongmai (1)
- year (1)